How AI Can Assist in Creating a State of the Art
Writing a State of the Art:
A state of the art is a synthesis of current knowledge on a given topic, bringing together studies and advancements in the field. It’s a vital step for researchers, professionals, and students, as it keeps them informed, aids in making informed decisions, and enhances their understanding of the subject at hand.
Steps for Writing a State of the Art:
Defining the Topic
Collecting Sources
Using Databases
Establishing Selection Criteria
Analyzing Documents
Organizing Information
Identifying Trends and Gaps
Comparing and Synthesizing
Presenting Results
Citing Sources
Read more
2. AI at the Service of the State of the Art
There are many advantages to using artificial intelligence to produce a state of the art. Artificial intelligence can be used at all the key stages in the preparation of the state of the art to speed up the process, increase reliability and improve the quality of the document.
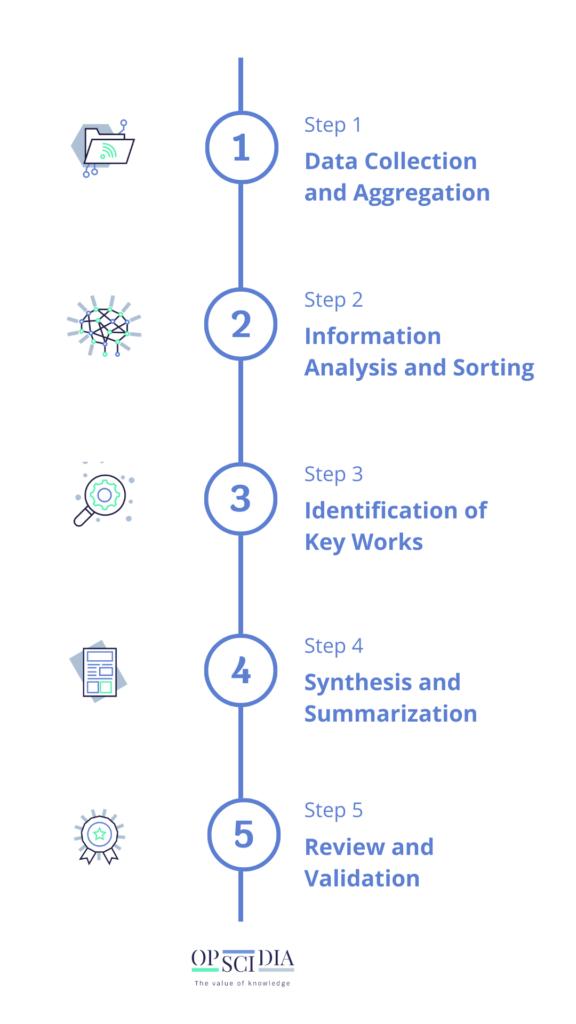
AI-Assisted State of the Art Creation Involves:
1. Data collection and aggregation: Using AI technologies, it is possible to aggregate the data present in databases to create an organised and reliable knowledge base on a subject of study.
2. Analysing and sorting information: Natural language processing (NLP) combined with text analysis and information sorting techniques can be used to understand the content of the documents collected. These technologies can then be used to sort the relevant information according to the criteria defined.
3. Identification of key works : AI-assisted bibliometric analysis identifies key works and the most influential publications in the field under study.
4. Synthesis and summary: AI, thanks to automatic natural language processing (NLP), is able to synthesise the information collected to create a clear and concise summary of the state of research in the field.
5. Review and validation: Although AI is capable of rapidly collecting and analysing large volumes of data, human review remains essential to verify the relevance and quality of the information collected.
3. AI Tools for Crafting a State of the Art
Here’s an AI tool for each phase of state-of-the-art development :
Step 1
Data Collection and Aggregation
OpenAlex software can aggregate data from various academic sources, databases, and publications to create an organized knowledge base.

Step 2
Information Analysis and Sorting
GPT-3‘s natural language processing system can understand document content and sort relevant information.

Step 3
Identification of Key Works
CiteSeerX identifies influential works through citation and reference analysis.
Step 4
Synthesis and Summarization
IBM Watson’s automatic summary tool synthesizes research information into concise summaries.

Step 5
Revision and validation
The Zotero bibliographic reference management tool facilitates collaboration and human revision by enabling researchers to check the relevance and quality of the information they collect.
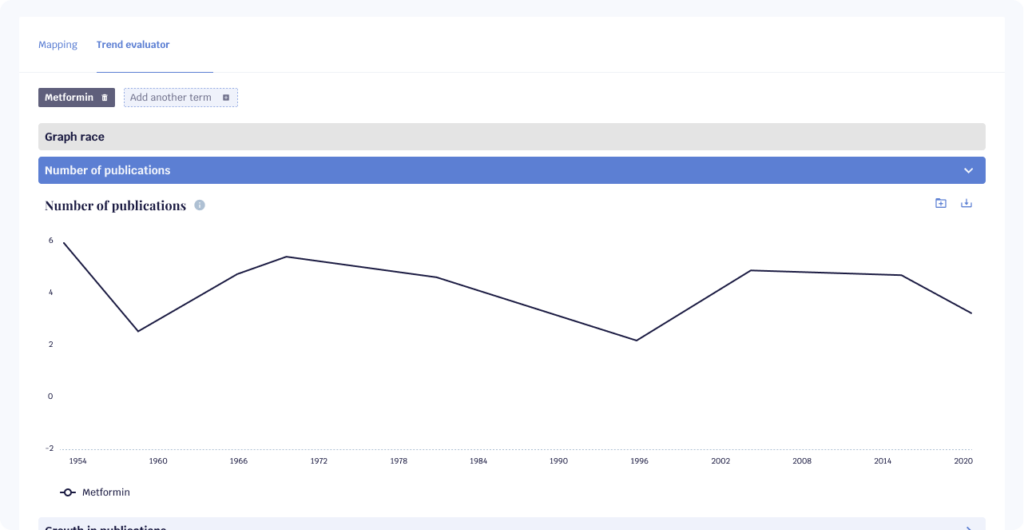
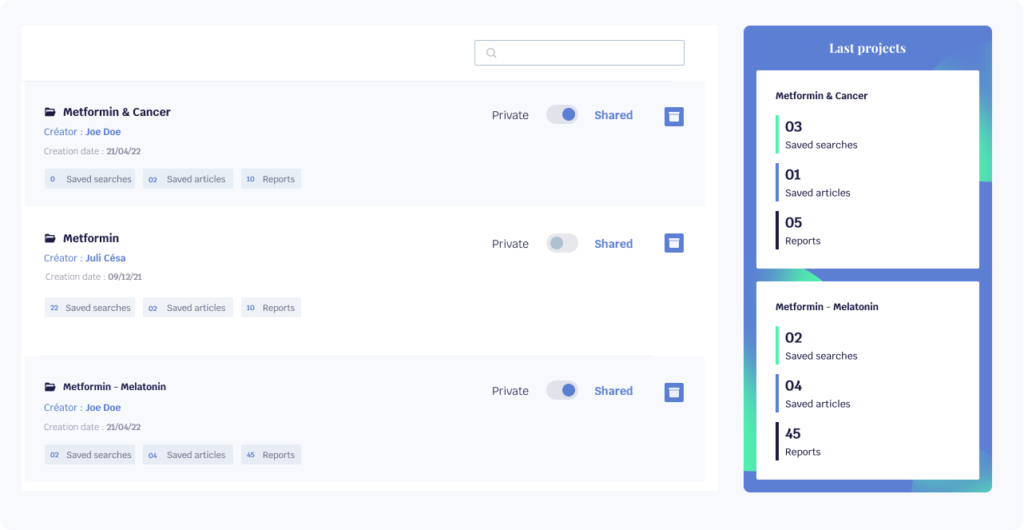
There is such a thing as a single, comprehensive tool that optimises all the stages involved in creating a state of the art!
Find out how the Opscidia application can transform your state-of-the-art writing!
Step 1
Data Collection and Aggregation
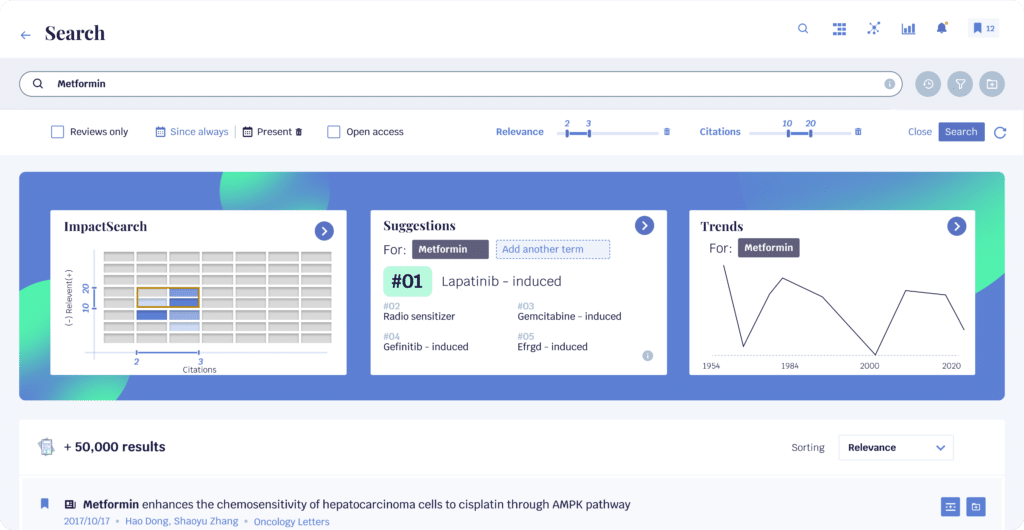
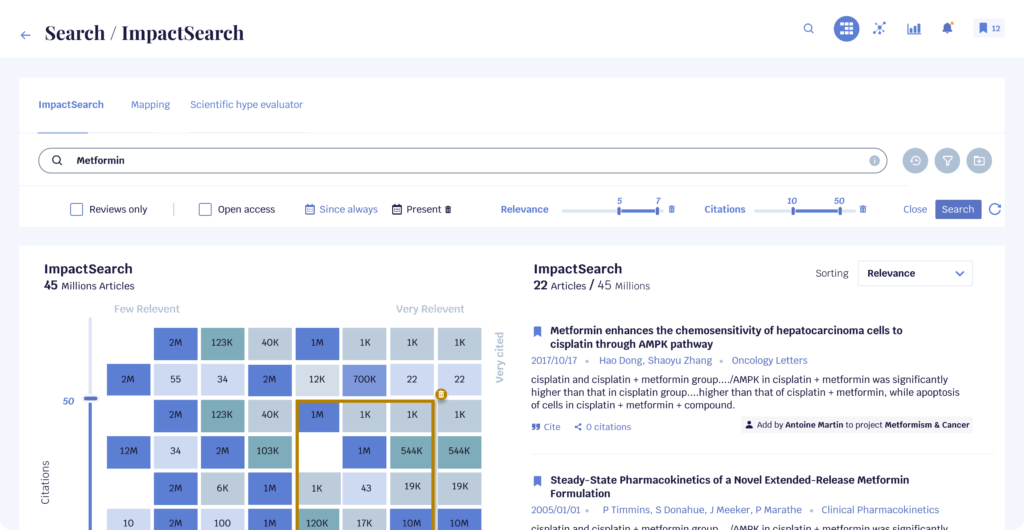
Explore over 150 million scientific articles, patents and scientific journals using our powerful scientific search engine.
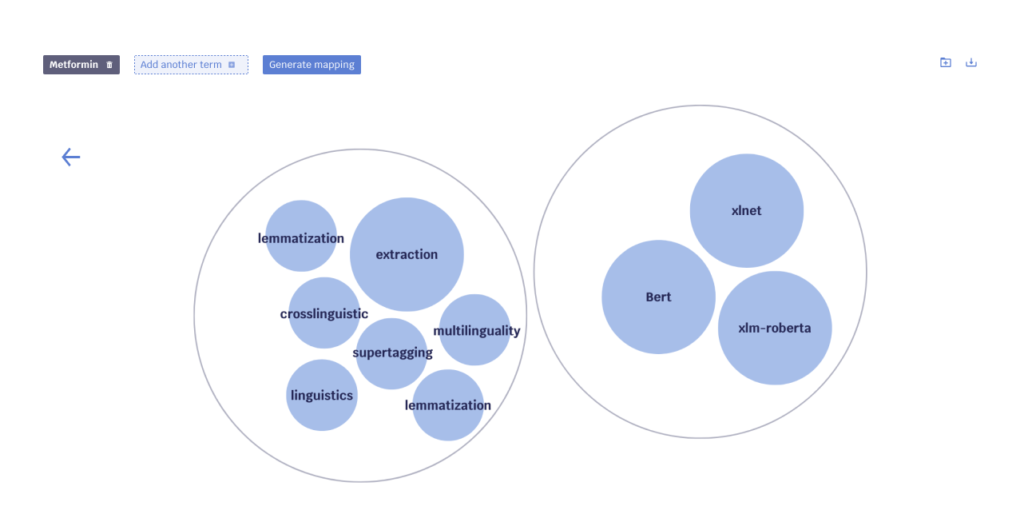
Step 2
Information Analysis and Sorting
Our brand new scientific report generation functionality creates coherent clusters from the articles you have selected, saving you valuable time.
Step 3
Identification of Key Works
With Opscidia Impact Search, find relevant documents twice as fast. Our ranking of search results is based on the number of citations and the relevance of the document.
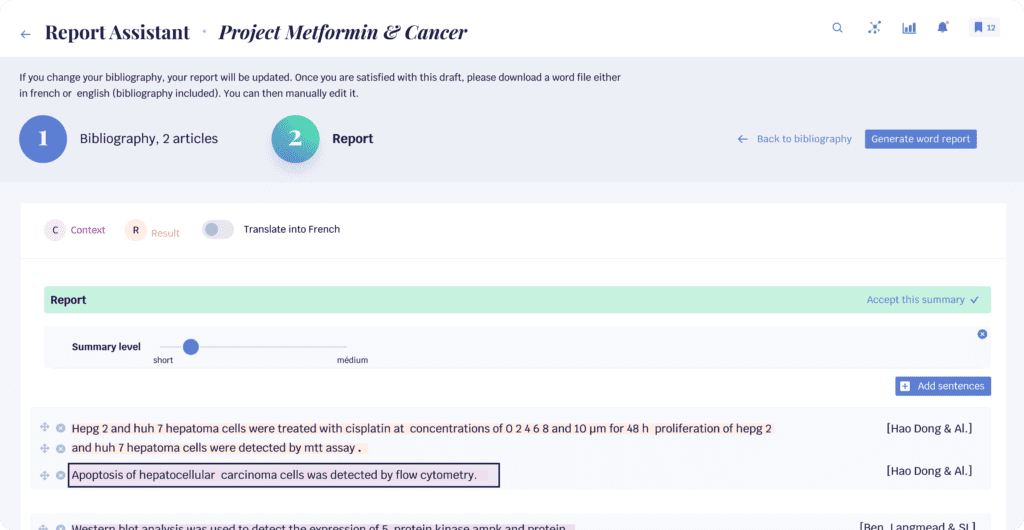
Étape 4
Synthesis and Summarization
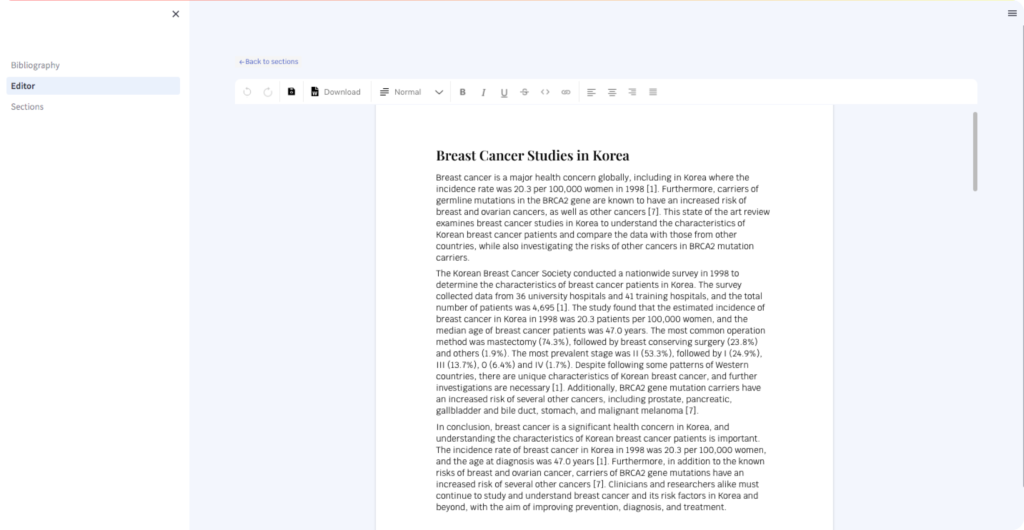
Use our report assistant tool to select your documents, and let AI generate a structured and coherent synthesis in just a few clicks.
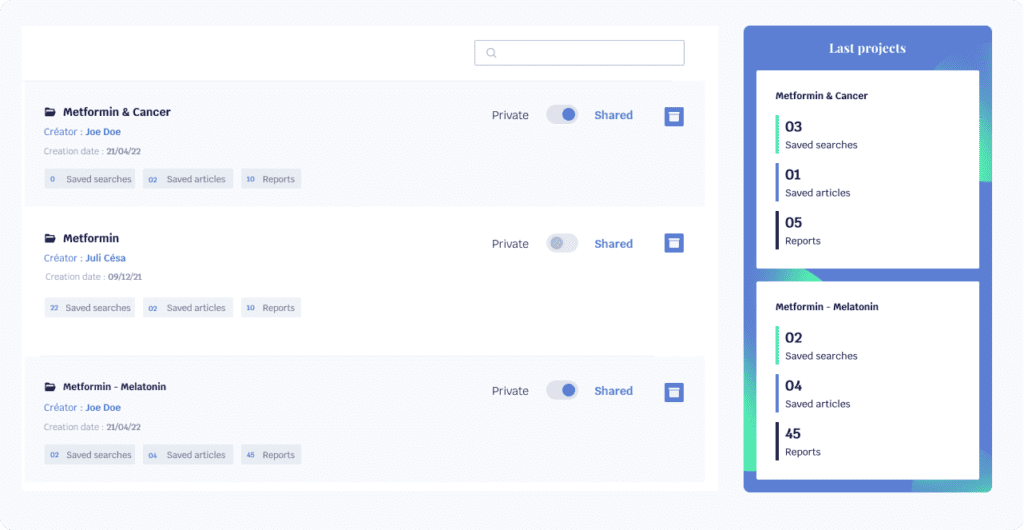
Étape 5
Revision and validation
Thanks to our collaborative projects feature, share the state of the art with the stakeholders of your choice. You can interact by liking, commenting and creating alerts for an efficient validation process.
4. AI best practice in the state of the art
Select Appropriate Algorithms: Choosing the right AI algorithms for analyzing and synthesizing scientific data ensures relevant and reliable results.
Human Validation: While AI can do much of the work, human validation is crucial to verify information quality and prevent misunderstandings.
Use Reliable Sources: Ensuring AI relies on trustworthy databases and scientific sources guarantees the validity of collected and synthesized information.
5. Limits of AI in the State of the Art:

Contextual Understanding: AI may struggle with understanding the specific context of a research field, leading to misinterpretations.
Data Bias: If AI training data is biased, it can affect results, leading to partial or incorrect conclusions.

Language Limitations: AI may struggle with complex or ambiguously defined concepts in scientific documents, affecting synthesis quality.
Lack of Critical Judgment: Unlike human expertise, AI can’t exercise critical judgment on source quality, potentially overvaluing certain information.
Discover all the features designed to accelerate your technology intelligence thanks to AI.

6. Case study: Example of a state of the art carried out with the assistance of AI
Facial Recognition
Masked Face Recognition and Privacy Protection in Authentication Systems
Masked face recognition and privacy protection in authentication systems is a crucial area of research. With the advancement of facial recognition technology and the increasing use of face recognition in various domains such as casino management systems, smart home environments, and event venues, the need to address the challenges related to recognizing masked faces and ensuring privacy protection has become imperative [1] [3] [5] .
Facial recognition systems are being used in networked casino management computer systems to identify players based on their facial images and record their activities [1] . In smart home environments, electronic greeting systems with facial recognition capabilities are employed to detect and respond to visitors approaching the entryway [3] . Event venues utilize facial recognition to capture event occurrences and the reactions of eventgoers, enabling the identification of specific individuals in photos or videos [5] .
These applications highlight the need to address the issues of recognizing masked faces, as masks can hinder accurate facial recognition. Additionally, privacy concerns arise with the use of facial recognition technology, especially in public spaces. The methods proposed in these studies aim to tackle these challenges.
In the casino management system, the facial recognition system accesses a biometric database to match the received facial image, while the casino management server identifies the player record and records the activity of the associated device [1] . The smart home environment’s electronic greeting system initiates facial recognition while the visitor approaches the entryway and incorporates context information from sensors to determine an appropriate response [3] . Event venues use facial recognition to identify eventgoers in photos or videos captured during event occurrences and send personalized content to the identified individuals [5] .
The use of facial recognition technology in various domains presents both opportunities and challenges. While it enhances security and convenience, recognizing masked faces and safeguarding privacy are important considerations. The research discussed in these articles addresses these concerns by proposing methods to improve masked face recognition and protect privacy in authentication systems. Further advancements in this field will contribute to the development of more efficient and secure authentication systems.
Facial Recognition for Enhanced Security and Authentication
Facial recognition technology has become increasingly prevalent in various applications, such as authentication and attendance tracking. However, the use of face masks due to the COVID-19 pandemic has posed a challenge to the accuracy of these systems. This paper aims to address this issue by proposing a methodology that incorporates masked faces into existing facial datasets, allowing for accurate recognition without the need for recreating user datasets. The proposed approach includes an open-source tool called MaskTheFace, which effectively masks faces and generates a large dataset of masked faces. This dataset is then used to train a facial recognition system that demonstrates improved accuracy for masked faces.
The use of face masks as a preventive measure during the COVID-19 pandemic has raised concerns regarding the accuracy of facial recognition systems used for authentication and attendance tracking [2] . Due to the obstruction caused by face masks, these systems may fail to detect and recognize individuals, rendering existing datasets invalid and rendering the facial recognition systems inoperable. To address this issue, the paper presents a methodology that utilizes the current facial datasets by augmenting them with tools that enable the recognition of masked faces with low false-positive rates and high overall accuracy, without requiring the recreation of user datasets [2] .
The paper introduces an open-source tool called MaskTheFace, which is designed to effectively mask faces and generate a large dataset of masked faces. This tool enables the training of a facial recognition system specifically tailored for recognizing masked faces. The effectiveness of the proposed methodology is demonstrated by reporting an increase of 38% in the true positive rate for the Facenet system [2] .
To further validate the accuracy of the retrained system, the paper conducts tests on a custom real-world dataset called MFR2. The results show similar levels of accuracy, confirming the effectiveness of the methodology [2] .
In conclusion, the paper addresses the challenge posed by face masks on facial recognition systems by proposing a methodology that incorporates masked faces into existing datasets. By using the MaskTheFace tool to generate a large dataset of masked faces and retraining the facial recognition system, the accuracy for recognizing masked faces improves significantly. This approach allows for the utilization of existing datasets without the need for recreating user datasets, ensuring the continued operability of facial recognition systems in the presence of face masks [2] .
In conclusion, the paper presents a methodology to overcome the accuracy challenge faced by facial recognition systems due to the use of face masks. The proposed approach incorporates masked faces into existing datasets, allowing for accurate recognition without the need for recreating user datasets. By utilizing the open-source tool MaskTheFace to generate a dataset of masked faces and retraining the facial recognition system, significant improvements in accuracy are achieved. The methodology is validated through experiments, reporting an increase in the true positive rate of the Facenet system and demonstrating similar levels of accuracy on a real-world dataset. Overall, the proposed methodology provides a practical solution for maintaining the operability of facial recognition systems in the presence of face masks [2] .
References